
The attackers changed how they usually do things, which made them even more dangerous.
Cryptojacking hackers from the Kinsing group are now actively using Looney Tunables (CVE-2023-4911), a Linux vulnerability that was found in October, to launch attacks that get into cloud environments. This is what the cloud security company AquaSec says.
The researchers' study is the first case of active use of Looney Tunables that has been made public. It shows how an attacker was able to get root access to the target environment.
Someone in the new campaign is using an old PHPUnit vulnerability (CVE-2017-9841) that lets anyone run any code. Since at least 2021, Kinsing has been using this method to get into different systems for the first time.
In the most recent attacks, hackers used a Proof of Concept (PoC) exploit in Python that was made public on October 5th by a researcher going by the name bl4sty. After this, the Kinsing hackers set off another PHP exploit, which, after being decoded, turned out to be JavaScript meant to be used for more attacks.
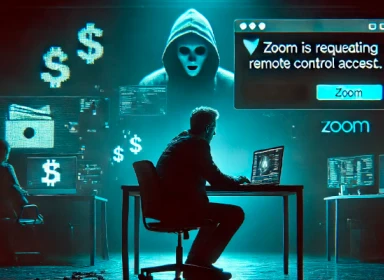
Attackers could manage files, run commands, and gather information about the device using this JavaScript code as a web shell.
The attack's main goal is to get cloud service provider credentials that can be used for further actions. This goal is different from what the Kinsing group usually does, which is to spread malware and run cryptocurrency miners.
However, the researchers say that this could mean that the group's operations are expanding. This could mean that in the near future, their activities will become more varied and intense, which will make cloud environments more vulnerable.




Comments 0