A single click during a video call is costing crypto investors hundreds of thousands of dollars.
The Exploit Behind the Call
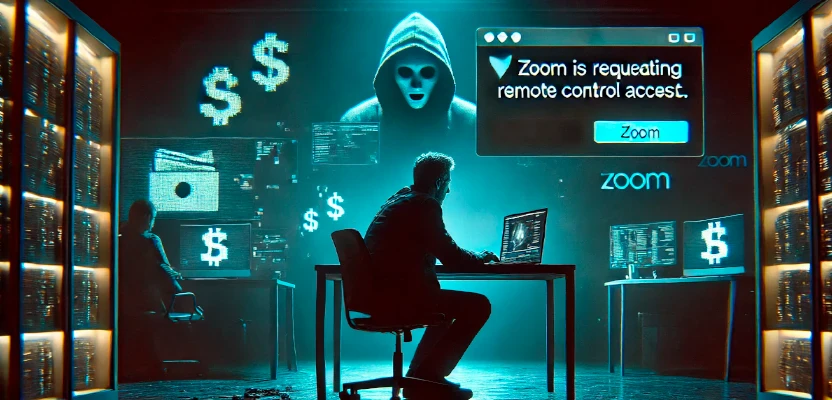
Zoom, once a hallmark of remote collaboration, has become the latest weapon in a sophisticated cybercrime campaign. Attackers are exploiting Zoom’s built-in remote control feature—a function designed for technical support or joint presentations—to hijack devices and drain digital wallets. This isn’t about code vulnerabilities. It’s about human behavior.
The feature allows one user to request control of another's device during a screen share. It’s a handy tool in the right hands—but in the wrong ones, it becomes a gateway to disaster.
Meet ELUSIVE COMET
The group behind the attack has been tentatively named ELUSIVE COMET by The Security Alliance (SEAL), a nonprofit watchdog focused on cybersecurity in the crypto space. Their tactics blend technology, deception, and social engineering into a convincing trap.
Their cover? They pose as representatives of a fake venture capital firm called Aureon Capital, as well as its sister brands—Aureon Press and The OnChain Podcast. With professional websites, polished branding, and active social media accounts, they appear legitimate enough to fool even experienced professionals.
The Bait: A Podcast Invite
The con begins with a direct message or email. Victims—often entrepreneurs or developers in the crypto and Web3 community—are invited to appear as guests on The OnChain Podcast. The invitation comes with compliments, casual small talk, and eventually, a calendar link to schedule the Zoom call.
Once on the call, the victim is asked to share their screen—usually to discuss their latest project or a pitch deck. As the conversation flows, the attacker submits a remote control request. But here’s the twist: the attacker changes their Zoom display name to “Zoom,” mimicking a system prompt.
So instead of “John is requesting remote control access,” the message reads, “Zoom is requesting remote control access.” It looks official. Many victims click “Allow” without a second thought.
Real Losses, Real Victims
Jake Gallen, the creator of the Emblem Vault NFT platform, was one of those victims. He didn’t realize he had handed over control. By the time he noticed something was wrong, the attacker had installed malware and siphoned off around $100,000.
Another target—Dan Guido, head of cybersecurity firm Trail of Bits—was luckier. He and his team spotted red flags: inconsistencies in the attacker’s LinkedIn profile, reluctance to communicate via email, and phony calendar links. They walked away before any damage was done.
The Technology Isn't Broken—The People Are Being Tricked
The most alarming part? In many Zoom setups, remote control permission is enabled by default. Unless a user manually disables it, it remains an open backdoor.
This attack isn’t exploiting software bugs. It’s exploiting people. Distraction, trust in the interface, and split-second decisions are the real vulnerabilities.
“This isn’t about hacking Zoom,” says SEAL’s advisory. “It’s about hacking users’ habits.”
SEAL’s Advisory: What You Need to Know
SEAL has issued an official warning about ELUSIVE COMET. They’ve confirmed the group is behind millions in losses and remains active, well-organized, and dangerous. Their success lies in the illusion of legitimacy.
Here’s how they operate:
- Build Credibility
ELUSIVE COMET maintains detailed, convincing profiles across multiple platforms. They impersonate real people and create fake firms that pass a surface-level background check. - Make the Approach
The first contact is subtle—a podcast invitation via X (formerly Twitter) or email. Once accepted, they press for a quick Zoom meeting, sometimes delaying details to increase urgency. - Exploit Trust During the Call
Victims are prompted to screen-share. Then comes the request for control, disguised as a system message. If granted, the attacker installs either: - An infostealer: Immediately extracts data, crypto keys, and logins.
- A Remote Access Trojan (RAT): Allows for long-term surveillance and delayed exfiltration.
Prevention Tips: Don’t Get Caught Off Guard
SEAL offers clear recommendations:
- Verify Identities
Don’t rely on a LinkedIn profile or Twitter account alone. Cross-check with independent sources. Reach out via official company channels. - Use Trusted Platforms, Cautiously
Zoom, Google Meet, and Microsoft Teams are all widely used—but no platform is safe from social engineering. Always remain alert. - Disable Remote Access by Default
Zoom users can disable this feature in their settings. Organizations can enforce this at the admin level across all accounts. - Watch for Behavioral Red Flags
Hesitation to communicate over email. Scheduling links that feel off. Requests that create urgency. These are all signs something might be wrong.
A Message from the Victims
In a public thread that drew over 500,000 views, Gallen said he never consciously approved remote access.
“I don’t remember clicking anything. No signs popped up. It just happened,” he wrote.
He’s since been in contact with Zoom and hopes that the growing visibility of the scam will push for change—not just in settings, but in how users are protected.
Since going public, dozens of other victims have come forward. Some lost as much as $400,000.
Final Thoughts
This attack isn’t just about one platform or one group of victims. It’s a wake-up call for the entire crypto and tech community. We often talk about protecting code, securing endpoints, encrypting data. But when the weakest link is the person behind the screen, no firewall can help.
Awareness, caution, and a healthy dose of skepticism may be the best defense we’ve got.




Comments 0