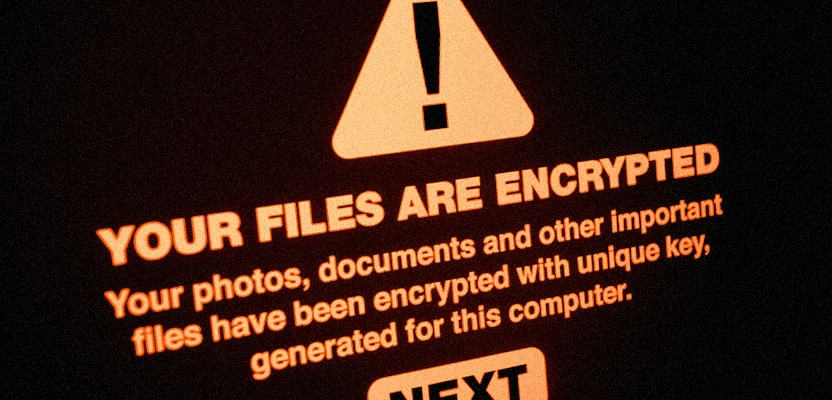
FIN7, a well-known cybercriminal group, advertises its AvNeutralizer tool (also known as AuKill) on underground Dark Web forums. This highly specialized tool is used by ransomware groups such as AvosLocker, Black Basta, BlackCat, LockBit, and Trigona to bypass security systems.
According to a SentinelOne report, AvNeutralizer is sold on the criminal underground and is widely used to interfere with security systems. FIN7, an electronic crime group of Russian and Ukrainian origin, has been active since at least 2012. Initially, they targeted point-of-sale (PoS) terminals, but later shifted to operating as an affiliate of groups such as REvil and Conti, and later launched their own ransomware, DarkSide and BlackMatter.
Also known as Carbanak, Carbon Spider, Gold Niagara, and Sangria Tempest (formerly Elbrus), FIN7 members created shell companies such as Combi Security and Bastion Secure to engage software engineers in their ransomware schemes under the pretext of penetration testing. Over the years, FIN7 has demonstrated a high level of adaptability by modernizing its arsenal of malware such as POWERTRASH and DICELOADER.
Attackers also conduct large-scale phishing campaigns using thousands of fake domains that mimic legitimate media and technology companies. These domains are used to redirect users to fake login pages masquerading as legitimate portals. They are also advertised on search engines such as Google, forcing users to download malware instead of popular software such as 7-Zip, PuTTY, Notepad++, and others.
It is worth noting that the use of FIN7 malware tactics was highlighted by eSentire and Malwarebytes in May 2024. The attacks led to the deployment of NetSupport RAT. FIN7 rents dedicated IP addresses from several hosts, but mostly from Stark Industries, which has been linked to DDoS attacks in Ukraine and across Europe.
Since the beginning of 2023, ransomware groups have started using updated versions of AvNeutralizer. This tool uses anti-analysis techniques and the built-in Windows driver to interfere with security solutions. It has been in active development since April 2022 and uses methods similar to those of the Lazarus Group, making it even more dangerous.
In addition, FIN7's updated Checkmarks platform includes a module for automated SQL injection attacks. The use of such methods significantly increases the group's influence.
AvNeutralizer's advertising on underground forums shows the evolution of FIN7's tactics, which now include selling the tool to other cybercriminals. The tool is becoming a valuable asset for attackers facing advanced defenses.




Comments 0