The ability to remain anonymous has emerged as a crucial component of personal security in this age of digital technology. It enables us to maintain the confidentiality of personal information, thereby shielding us from any potential dangers. However, just like everything else in this world, anonymity has a counterpart known as de-anonymization at the other end of the spectrum. The purpose of this post is to explain to you how the process of de-anonymization works and why it is essential for all of us to be aware of it.
What does it mean to deanonymize?
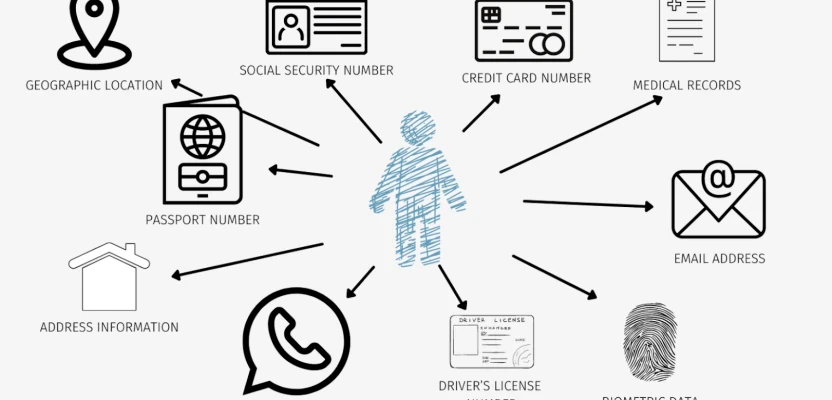
When an individual or organisation is hiding behind an anonymous identifier or pseudonym in the digital space, the process of deanonymization is the process of determining the identity of that individual or organisation. The disclosure of personal information may include the disclosure of one's name, address, telephone number, and other details.
This is how it operates.
Deanonymization can be accomplished through a variety of approaches, including but not limited to the following:
- The term "data correlation" refers to combining various pieces of data from various sources to form a complete picture. One example is when an individual uses the same username across multiple platforms; this allows for the collection of information from all of those sources, which can then be used to identify the individual.
- Analysis of Traffic: Conduct an analysis of network traffic in order to recognise distinctive patterns that may be connected to a particular user or group of users of the network.
- Statistical analysis is the process of analysing large data sets using statistical methods in order to identify distinctive characteristics that can be used to facilitate the identification of individuals.
What makes it so significant?
- By gaining an understanding of the process of de-anonymization, you will be able to better protect your personal data while you are using the internet.
- Privacy Policy: If you are aware of the ease with which data can be de-anonymized, it is possible that your perspective on privacy policies will change, and you will be more cautious about the platforms and services that you use.
- Public Awareness: Providing more information about the issue of de-anonymization will assist in the development of a society that is more aware and able to make well-informed decisions regarding its cybersecurity.
The process of deanonymization is not merely a technical one; rather, it is a matter that concerns both our individual and collective safety in the contemporary digital world. The greater our knowledge and comprehension of this process, the better we will be able to safeguard ourselves against any potential dangers that may arise.



Comments 0