
The Darknet, a mysterious and often misunderstood corner of the internet, has gained notoriety for being a hub of illicit activities. However, beneath its shadowy reputation lies a realm that can be harnessed for both legal and illegal purposes.
A closer look at the Dark Web
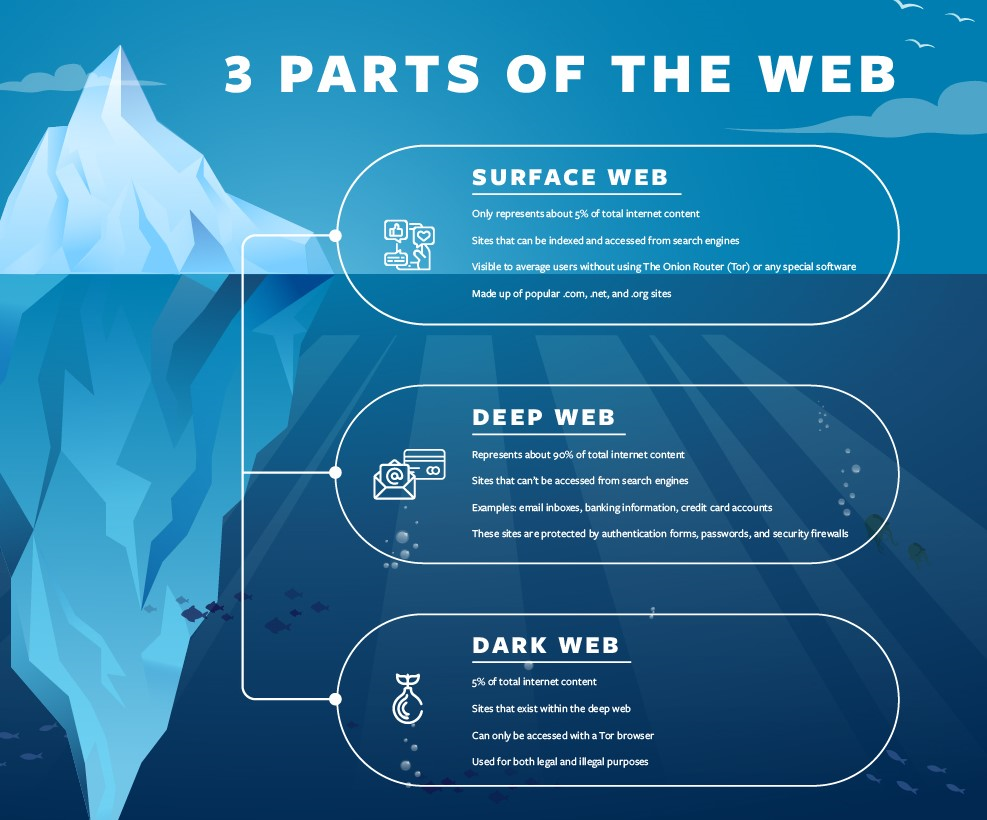
The term "dark web" refers to an obscured network existing beneath the surface of the internet. Comprising a series of concealed websites, it remains inaccessible through traditional search engines such as Google. This clandestine digital space operates differently from the mainstream internet, drawing information from sources beyond the reach of conventional search engines. These sources include content from individual accounts like email, social media, banking, personal and professional databases, and legal and medical documents.
Also known as the darknet, the dark web bears similarities to the early days of the broader web during the late 20th century. The quality of content on the dark web is often amateurish, yet it provides an easier platform for individuals to establish sites and gain attention. Notably, tech giants and large media organizations wield minimal influence over this network.
While the dark web has gained notoriety as a hub for illegal activities, mirroring the early internet's reputation, it serves as a social outlet for individuals facing persecution for their identities or political beliefs. Additionally, it offers legal authorities supplementary tools to apprehend those engaged in unethical activities.
History of the Dark Web
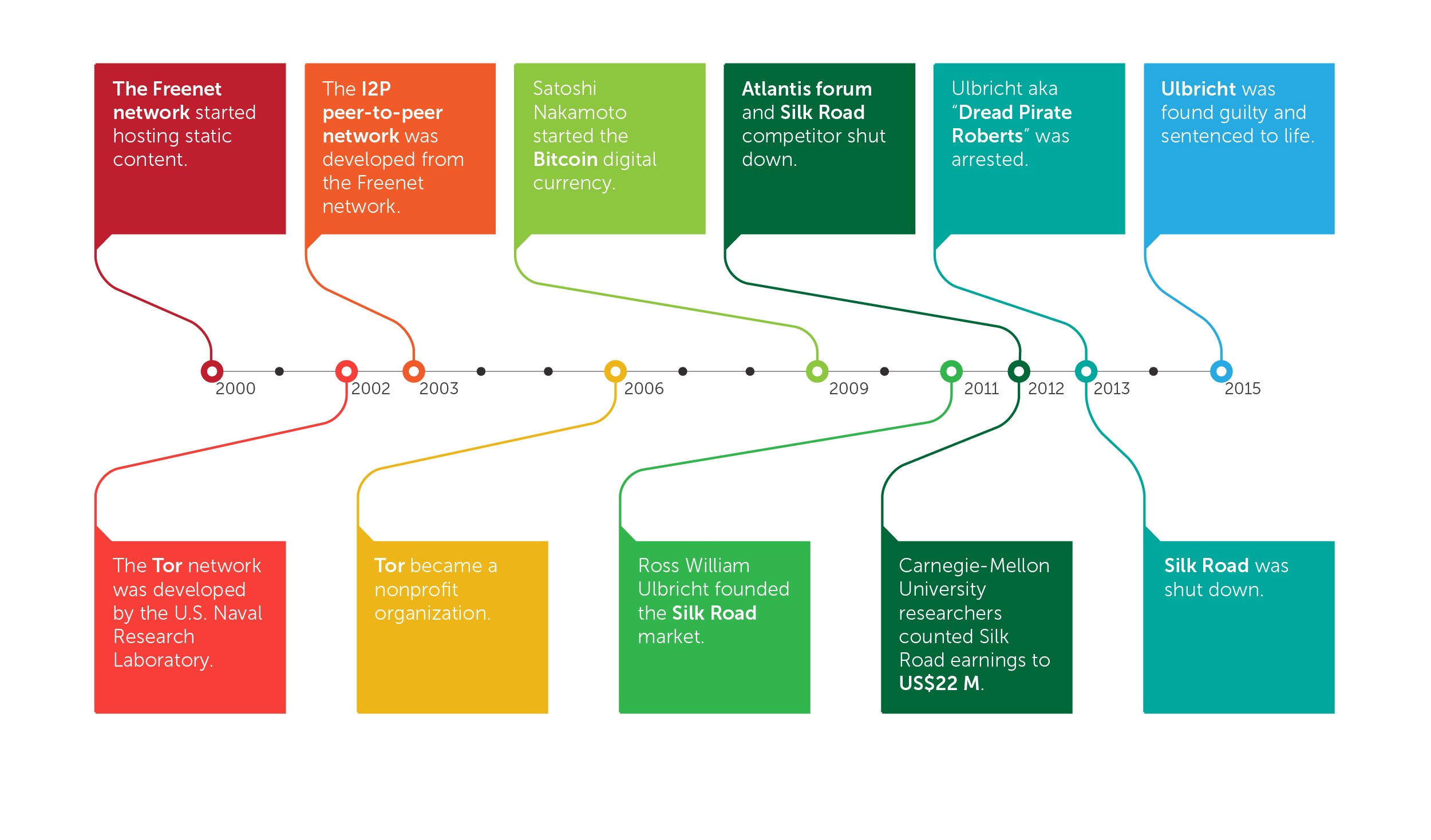
The dark web officially emerged in the early 2000s with the development of Freenet by Ian Clarke. Freenet aimed to provide users with a secure platform, shielding them from government intervention and cyber attacks. This system, still operational today, enables users to express themselves freely without online tracking.
The U.S. Naval Research Laboratory played a pivotal role in funding The Onion Router (TOR) project, a browser designed to facilitate secure communication, particularly in hostile environments where personal safety is a primary concern. TOR has evolved into one of the most commonly used browsers for accessing the dark web, leveraging databases to assist users in navigating and obtaining the information they seek.
The surge in popularity of cryptocurrencies has significantly contributed to the dark web's appeal, particularly for cybercriminals. Digital currencies offer a level of anonymity that is attractive to those engaging in transactions within the shadows. However, the association of the dark web with certain illicit activities has prompted calls for its regulation. International bodies such as the G20 and the Financial Action Task Force (FATF) have advocated for increased scrutiny of cryptocurrency companies, urging them to disclose information about buyers and sellers involved in online transactions. The objective is to empower law enforcement in tracking criminal organizations and curbing illicit activities associated with the dark web.
Advantages and Disadvantages of the Dark Web

Advantages
The dark web is often hailed for its role in safeguarding privacy and enabling unrestricted expression of views. This is particularly crucial for individuals facing threats from stalkers and criminals, offering them a secure space to navigate the digital realm. Moreover, as employers increasingly scrutinize social media posts, the dark web provides a haven for genuine, private discussions that might otherwise be stifled.
Interestingly, the dark web's popularity among criminals inadvertently facilitates undercover police communication, presenting law enforcement with a covert means of interaction.
Disadvantages
However, the inherent anonymity and privacy of the dark web can be exploited, leading to a surge in criminal activities. The synergy between the dark web and cryptocurrencies, for instance, creates an environment conducive to hiring individuals for illicit purposes.
Despite its commitment to user privacy, the dark web also becomes a breeding ground for privacy violations. Instances of private photos, medical records, and financial information being stolen and circulated on the dark web underscore the potential misuse of this covert platform.
Legal dimensions of the Dark Web
It's crucial to dispel the notion that everything on the dark web is inherently nefarious or against the law. Originally established as an anonymous communications channel, the Tor network continues to serve a valuable purpose by facilitating communication in environments where free speech is under threat. Particularly in countries with eavesdropping or criminalized internet access, individuals turn to the dark web for secure communication.
For those seeking knowledge on privacy protection or cryptocurrency, the dark web offers a spectrum of resources. Private and encrypted email services, tutorials on installing anonymous operating systems, and advanced tips for privacy-conscious individuals are among the offerings.
Surprisingly, the dark web isn't exclusively a hub for illicit activities. It hosts content akin to what you'd find on the public web, such as full-text editions of rare books, collections of mainstream political news, and even a guide to the steam tunnels under the Virginia Tech campus. Platforms like Intel Exchange allow anonymous discussions on current events, and there are dark web counterparts to whistleblower sites like Wikileaks. Established entities, including Facebook, have a presence on the dark web, indicating a growing awareness among legitimate web companies.
Beyond mere curiosity, the dark web holds practical value for certain organizations. Law enforcement agencies actively monitor it for stolen data from recent security breaches, aiming to trace a trail back to the perpetrators. Similarly, mainstream media organizations keep an eye on whistleblower sites on the dark web for potential news leads. The landscape of the dark web, while often associated with illicit elements, reveals a more nuanced and multifaceted space that extends beyond the boundaries of criminal activities.
Best ways how Dark Web can be used
1. Preserving privacy and anonymity
One of the primary legitimate uses of the Darknet is to provide individuals with enhanced privacy and anonymity. In environments where freedom of expression is restricted or monitored, the Darknet becomes a refuge for those seeking to communicate without fear of reprisal. Journalists, activists, and citizens in oppressive regimes can utilize the Darknet to express their thoughts, share information, and organize without the risk of government censorship. In addition, the Darknet offers individuals the ability to make purchases anonymously.
2. Secure communication and whistleblowing
The Darknet serves as a secure platform for communication, especially when confidentiality is paramount. Whistleblowers seeking to expose corruption or misconduct can use Darknet platforms to share information without revealing their identity. Secure communication tools and platforms hosted on the Darknet, such as SecureDrop, provide a safe space for individuals to disclose sensitive information to journalists and organizations.
3. Protection against surveillance
In an era of increasing surveillance, the Darknet offers a layer of protection against unwarranted monitoring. Privacy-conscious individuals can use Darknet browsers to access information without leaving a digital trail. This is particularly valuable for those seeking to shield their online activities from advertisers, trackers, and government surveillance.
4. Access to information in censored regions
The Darknet serves as a gateway to unrestricted information in regions where internet censorship is prevalent. Citizens facing restricted access to news, educational resources, or social media can use Darknet networks to bypass censorship and connect with the broader digital world. This function of the Darknet contributes to the promotion of free access to information.
5. Cybersecurity training and research
Legitimate cybersecurity professionals often utilize the Darknet as a controlled environment for training and research. Hacking competitions, simulated cyber-attacks, and forums dedicated to cybersecurity discussions provide a valuable space for honing skills and staying abreast of the latest developments in the field.
Conclusion
The dark web, though a relatively recent addition to the internet's vast landscape, offers a means of anonymity for those who wish to express themselves without fear of consequences. However, this heightened level of privacy has contributed to the dark web's negative image as a platform for illicit activities. Accessing the dark web involves installing a private browser, employing a VPN for added security, and ensuring the overall safety of your computer. While it provides a space for privacy, it's crucial to acknowledge the challenges and potential risks associated with its usage.



Comments 0